Hacker Pod2G developed the first iOS 5.01 Untethered Jailbreak and more recently has been known for being one of the head figures behind the iOS 5.1.1 Untethered Jailbreak. Today Pod2G has taken to his blog to alert the community to a flaw he found in iOS that he considers to be extremely severe.
Apparently this flaw has existed since the beginning of the implementation of SMS in the iPhone and even in the latest iOS 6 beta 4 firmware it is still present. What is this flaw? Well, before you can truly understand this flaw you need a little background information on how an SMS text works.
A SMS text is basically a few bytes of data exchanged between two mobile phones, with the carrier transporting the information. When the user writes a message, it is converted to PDU (Protocol Description Unit) by the mobile and passed to the baseband for delivery.
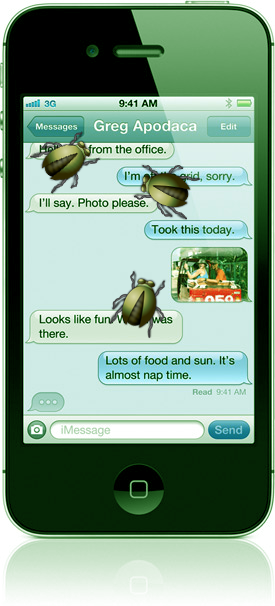
Essentially when you are composing or replying to an SMS message it needs to be converted to a format that the baseband can send to the receiving phone. The problem is, if you own either a smartphone or modem and an account in a SMS gateway you can send text messages in raw PDU that will allow you to spoof who the message was sent from.
In the text payload, a section called UDH (User Data Header) is optional but defines lot of advanced features not all mobiles are compatible with. One of these options enables the user to change the reply address of the text. If the destination mobile is compatible with it, and if the receiver tries to answer to the text, he will not respond to the original number, but to the specified one.
As Pod2G has outlined this could be a very bad flaw that pirates could use to their advantage to try to steal sensitive information from you. It also means people could be easily manipulated, thinking they are replying to someone or something that in reality they are not.
- pirates could send a message that seems to come from the bank of the receiver asking for some private information, or inviting them to go to a dedicated website. [Phishing]
- one could send a spoofed message to your device and use it as a false evidence.
- anything you can imagine that could be utilized to manipulate people, letting them trust somebody or some organization texted them.
Now that you are aware of this flaw in iOS, always ensure you double check to see the number you are replying to. As you never know if you could be victim to this severe SMS flaw.
why the hell would you, text your info to a bank. that is just stupid
You would be surprised what some people would do my friend… I have heard worse horror stories of people’s idiocy.