Since the release of the iOS 6.1 firmware came a whole new wave of lockscreen bugs that people brought to light on YouTube. Once Apple patched the lockscreen bug, there was another discovered in iOS 6.1.2 and now just a day after the release of iOS 6.1.3 another one has been found.
These lockscreen bugs ranged in severity, with the one found in iOS 6.1.2, perhaps the most worrying. The new lockscreen bug found in iOS 6.1.3 is probably the one that should worry you the least, but it is still yet another vulnerability you need to be weary about.
The way this lockscreen exploit works is by taking advantage of the Voice Dial functionality. The user simply initiates voice dial, says a command to call a number and once it starts calling you remove the SIM card. Doing this grants access to the Phone app and also the camera roll.
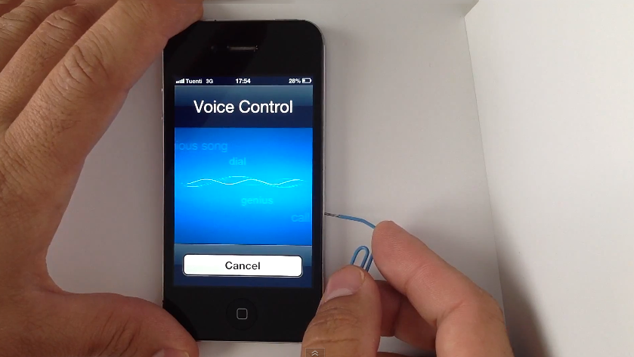
For devices with Siri enabled, this shouldn’t work and should only apply to those with Siri disabled (as Voice Control only activates when Siri is disabled). I have personally not experimented with this however, so I can’t confirm this. The founder of this lockscreen vulnerability says the flaw can be avoided by disabling the “Voice Dial” option.
Apple is not alone at experiencing issues with the lockscreen, in fact, one was found with the Samsung Galaxy S III that allowed access to the entire handset. These lockscreen bugs do not pose a huge security risk because an individual would actually need access to your device for an extended period of time, but it is still concerning.
well the video didnt show what software version is on the phone
Olly’s right, but this is still a useless lockscreen bug. I’d like to see one where you can actually access the entire phone itself, not just the phone.app