It was recently circulating around the web that a Swedish security firm, Micro Systemation had developed an application called XRY capable of cracking the passcode on your iOS device in under two minutes. The application could also log keystrokes and access personal data on your iOS device. The notion of this scared a lot of people, but in reality there is nothing to be afraid of.
As pointed out by 9to5Mac, hacker Will Strafach or @chronic has just posted his thoughts on this two-minute passcode unlock. Stating that the XRY program uploads a custom ramdisk that takes advantage of the LimeRa1n exploit created by GeoHot. This means it will not even work on the latest generation iOS devices like the iPhone 4S, iPad 2 and third-gen iPad.
Another interesting tid-bit of information left out by the security firm was that it takes two minutes to crack your iOS device’s passcode if it is “0000”. If you have any other combination other than “0000” it will take much longer. For those of you that are still worried that this could affect your older generation iOS device however, you will be glad to know some advice from Will Strafach was kindly given:
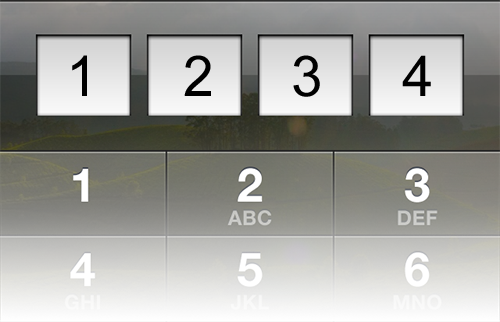
If you don’t feel like upgrading to the latest model and your device is exploitable, it is still possible to protect yourself from tools like this. Just open Settings on your device, then tap the “General” menu, then go into the “Passcode Lock” menu. You should see a switch labelled “Simple Passcode”. If you turn this off and then set a lengthier password to unlock your device, that’ll make it take much longer than two minutes to crack the passcode on your device (the longer, the better).
What are your thoughts about the XRY iOS passcode cracking application? Share your responses in the comments section below…
No one should be worried about this at all. Notice how the company doesn’t say how exactly this works?! I don’t know for sure but I’m guessing to put this on the I device you would need to plug in to a computer to put this app on the device or at the very least the device unlocked to install which would defiet the object. Wouldn’t it? No one is going to put this on there own phone and I think I would notice someone pluging my phone in to a computer. So I believe the company can do what they claim but it’s not as they claim. They would need access to your device for a lot longer than 2 minutes and possible need it unlocked to install the software so I wouldn’t worry
AFFECT, not EFFECT.
Yes, it bothers me. Lol.