Here at iJailbreak, we’ve covered a few methods for encrypting your personal information and messages in the past. One of the easiest and most secure methods that we’ve seen of keeping your messages private is Foxygram, but that app tries to prevent jailbroken iPhones from using it. If you’re interested in using an encryption scheme that will work with a jailbroken phone out of the box, Henri Gil has come up with two apps: Crypt 2.0 and its counterpart Decrypt 2.0.
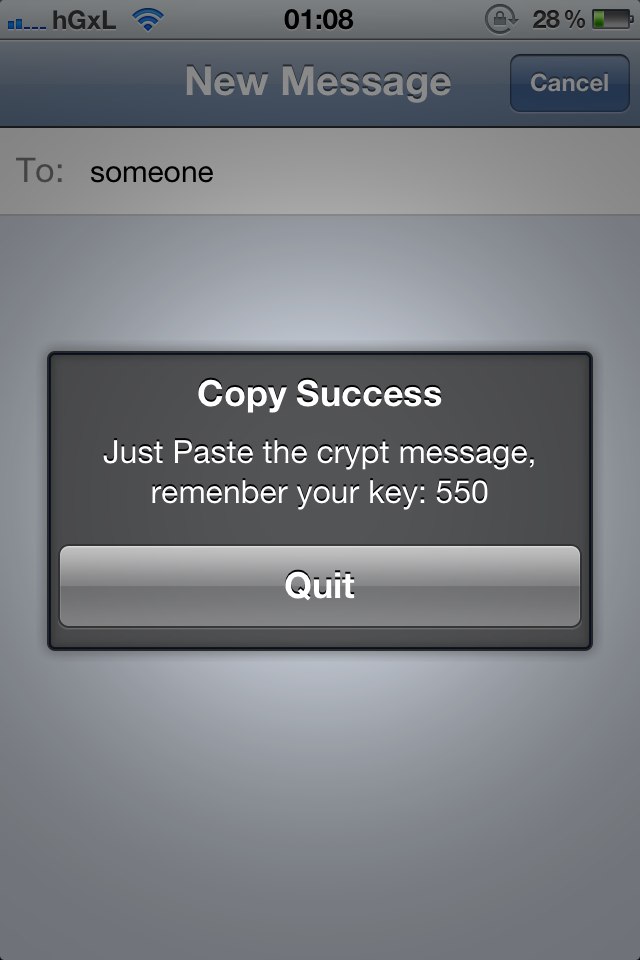
The encryption plugins work anywhere you can enter text. All you need to do is type in your message and highlight it, use the context menu (by default used for copy and paste), and select the option for Crypt 2.0. The program will ask you to remember the encryption key and will spit out a string of numbers. To turn the numbers back into text, highlight the message, activate Decrypt 2.0 from the context menu, and you’ll see the translated message in a dialog box.
The encryption keys are pretty simple, usually a value like “550”, which will be easy to remember and use, but I’m guessing will be less powerful than the military-grade encryption that other services offer (including services in the app store). Just a tip: you probably don’t want to send the encryption keys through the same channel you’re sending encrypted messages from.
Both plugins can be found in the BigBoss repository. Crypt 2.0 is a paid plugin, available for $1, while the decrypt plugin is free. That said, you might be better off duping Foxygram (freemium) into thinking your iPhone, iPad, or iPod Touch isn’t jailbroken with xCon (a free circumvention tweak). The encryption should be far stronger, to the point where MIT’s Technology Review fears it could lead to a future of untraceable criminal activity. But if you’re just trying to keep noisy friends from snooping around in your diary, Crypt 2.0 should provide more than enough cryptographical muscle.
How much cryptography do you need? Share your thoughts in the comments section below.

Is it hard for the developer to spell “Remember” correctly?
wich encryption does this use?