iWep Pro 5 is an application which, at least according to its Cydia page, is a password search tool for wireless routers. Supposedly it uses a form of key calculation on supported routers to crack the password, although I suspect it actually contains a library of default router passwords. This app could potentially be used for the purpose of gaining access to someone else’s private network, though the app contains a disclaimer that it’s meant for personal security use only.
At the very least, this won't present a problem for myself. What do I mean by that? Read on to see.
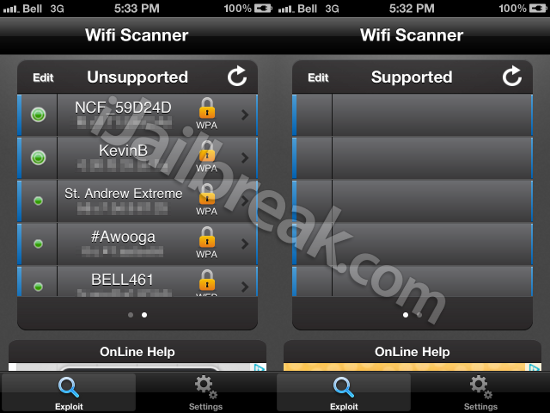
Since I’m not a total scumbag, I plugged in my own TP-Link modem and wireless router, as provided to me by the National Capital FreeNet (two more days until I’m hooked up with dry DSL, sigh) and fired up the app. As it turns out, the router FreeNet provided me is not one of the devices “compatible” with iWep Pro, and shows up in a list of unsupported devices along with every router in my neighborhood.
According to the developers page for an old version of the software, iWep Pro doesn’t work when the router’s factory settings were changed. What does that mean, exactly? Does that pertain to the router’s default password? The default name of the router? And if so, how does the “WEP/WPA key calculation” factor into the software?
Useful.
iWep PRO 5 is available in Cydia through the BigBoss repository and will tell you if your routers are supported by the exploit for free, however the app will only reveal your WEP/WPA key information for a “donation” of 5.50€ (about $7 US dollars). Since it doesn’t work with my router, or even any of the routers within WiFi range, I can’t vouch for the software.
Is your router more vulnerable than mine? Share your thoughts in the comments section below.
yeah yeah its NOT BACKTRACK MINI ,its bullshit,neither pirni and everything else,why should i say where the real one is
?>
Does that pertain to the router’s default password? yes
The default name of the router? yes
it has the algorythmes of routers their default names in relation with their default passwords..
so if you either changed the passkey or the name of the router it will not work..
it also doesnt work on every supported router.. their is a map on the maker’s website/facebook where u can see what routers in what countries are supported.
for me this just works fine.. and i only encounter the speedtouches and thomsons in my country.. i never seen any of the other router brands here lol
Where did you get the dictionaries ? I can’t get em from no where. The ones in cydia networking are giving an error of size missmatch .. PLz advice?
just got a email from the devellepor dis are taking off the cydia store so you have to install it with your mac or pc
its worthless to me as well. All networks are unsupported in my area. It is a money waste to me.
None of these softwares is working. I’ve tried almost everything and I came to the conclusion that only via pc (mac/linux) is possible to crack passwords. And if you don’t know how to do it exactly, you’re screwed.