Denial of Service (DoS) attacks involve sending large amounts of traffic to a service in hopes to crash it. Often times it is the number one weapon used to temporarily take down a website. Who would have guessed that Apple’s iMessage service could be targeted by a DoS attack though. According to The Next Web over the last couple of days well known developers in the Jailbreaking community and iOS developers in general have been targeted by a series of rapid-fire texts sent over Apple’s iMessage system.
Apparently the individuals behind these attacks simply setup an AppleScript that rapidly sends iMessages through the OS X Messages app to the target. As these messages build up, they can become so large that they can crash and lock up the Messages app on iOS, constituting a ‘denial of service’ (DoS) attack of sorts.
One of the individuals targeted include iH8Sn0w — the developer behind Jailbreak tools such as Sn0wbreeze — who said “On Wednesday night my private iMessage handle got flooded with “Hi” and “We are anonymous” bullshit.”
Grant Paul, otherwise known as Chpwn, was also targeted and said, “What’s happening is a simple flood: Apple doesn’t seem to limit how fast messages can be sent, so the attacker is able to send thousands of messages very quickly.” He further elaborated that if the user sends a ‘complex’ text message using unicode characters that force the browser to render Zalgo text, or simply uses a message that is enormous in size, then the Messages app will eventually crash as it fails to display it properly. This will effectively ‘break’ the Messages app on iOS by forcing it to close and stop it from re-opening because it can’t render that text.”
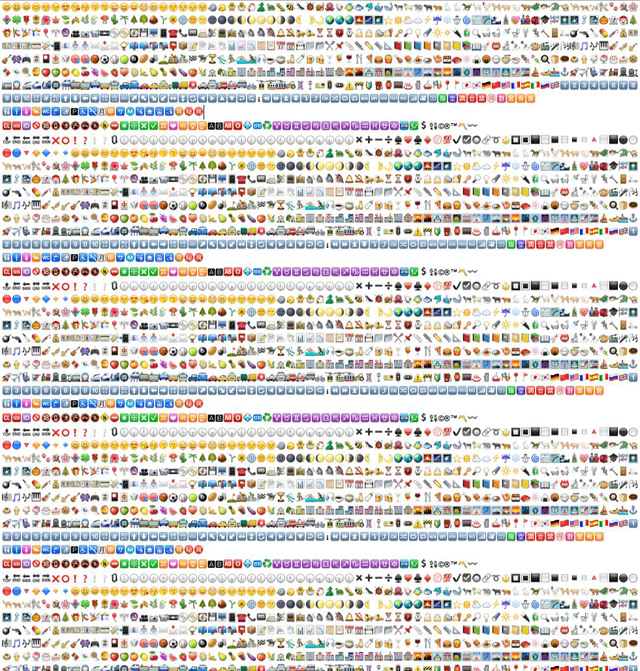
A selection of unicode that could crash the Messages app
Although this is unlikely to concern the everyday person, as Apple unifies your phone number and emails, it is important to remember that it is not hard for someone to ferret out your email to spam you with this annoying and disruptive technique. And considering Apple does not allow you to block specific iMessage senders, once your iMessage ID is out ,your only option would be to disable it entirely.
iH8Sn0w notes that Apple could take notice of these burst attacks and put blocks on repetitive spamming, but The Next Web could not get a comment from Apple directly on the matter.
Leave a Reply